The malware, discovered by cybersecurity firm ESET, was named NGate because it uses the NFCGate toolkit that attackers use to analyze NFC traffic. Czech police busted a gang using a similar scheme after arresting one of its members while he was trying to withdraw cash from an ATM in Prague. Here’s how the scam works: Victims receive a text with an urgent request to install an app because there is a problem with their tax return. The text contains a link to a fake website that harvests the victim’s credentials.
This gives attackers access to the victim’s bank account.
Victims then receive a call from the attacker posing as a bank employee. They are told that bank customers will receive a text containing a link to an app used to secure their accounts by changing their PIN and allowing them to verify their cards. Victims are asked to enable NFC on their phones and scan their cards. This mobile app was actually NGate malware.
The malware relays NFC data from the victim’s card via the compromised smartphone to the attacker’s smartphone, allowing the attacker to emulate the card, allowing the criminal to receive information in real time and withdraw cash from ATMs. Scary stuff, indeed.
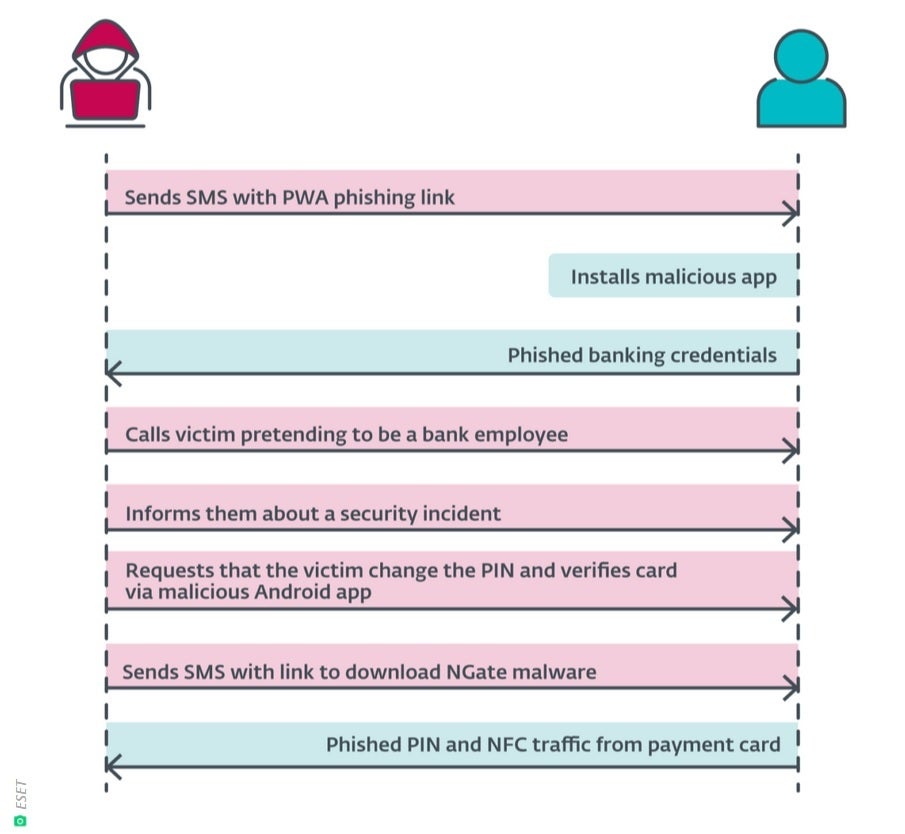
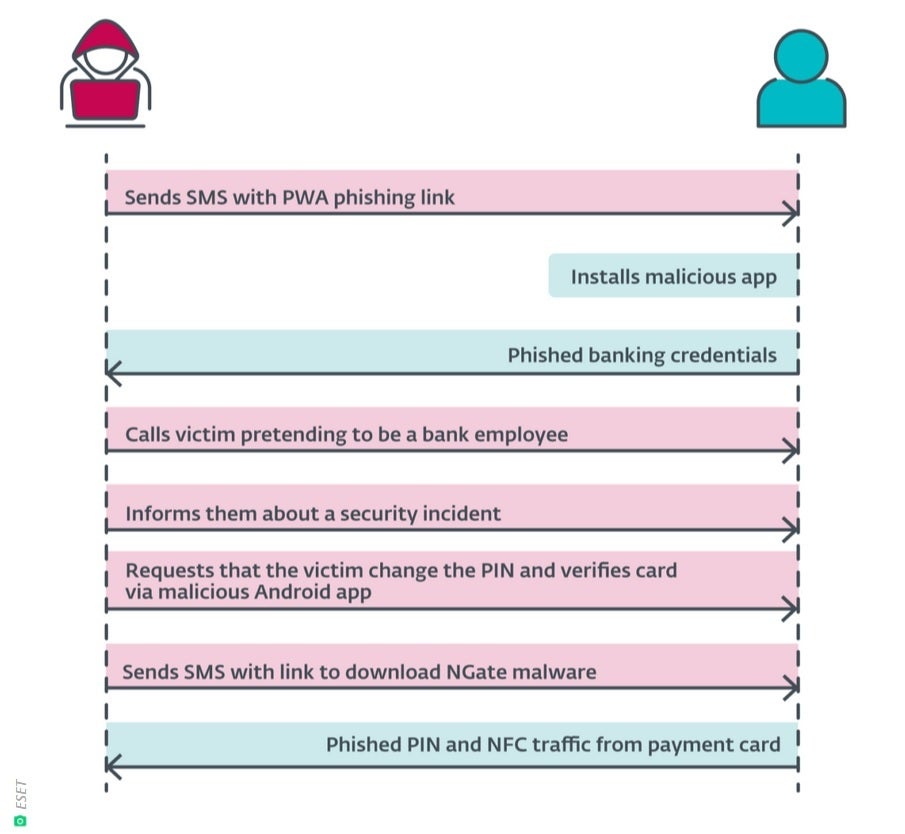
How the NGate malware attack works. | Image courtesy of ESET
“Based on current detections, no apps containing this malware were found on Google Play. Android users are automatically protected from known versions of this malware by Google Play Protect, which is enabled by default on Android devices with Google Play Services. Google Play Protect can warn users or block apps known to exhibit malicious behavior, even if they come from sources other than Play.” -Google
Google said it found no such malware in apps listed on the Play Store. Google noted that its Play Protect feature warns users and blocks apps that exhibit malicious behavior, even if they come from third-party sources. Between November and March, six NGate-powered apps that attacked three Czech banks were found from sources other than the Play Store.
How can you avoid becoming a victim? Never send any personal information online, including PIN numbers. Never hand over any personal information even if the text or email you receive seems legitimate. Always assume you are being scammed. If you are asked for information, call the company requesting it to verify. Get phone numbers from Google and never call numbers provided in texts.


