In August, hackers dumped 2.7 billion data records, including Social Security numbers, on a dark web forum, in one of the largest data breaches in history. The owner of the data, National Public Data Co., has now acknowledged the incident and blamed it on “third-party malicious actors” who hacked the company in December 2023.
The background check service acknowledged the breach in a statement posted on August 12. The company explained that it had taken “additional security measures” to prevent future incidents, but encouraged those affected to “take preventative measures” rather than offering any remedial measures.
Troy Hunt, a security expert and founder of the Have I Been Pwned breach checking service, investigated the leaked dataset and found that it contained just 134 million unique email addresses and 70 million rows from the U.S. criminal records database. The email addresses were not associated with SSNs.
Other records in the dataset include individuals’ names, mailing addresses and Social Security numbers, but some also contain other sensitive information, such as the names of relatives, according to Bloomberg.
How the data was stolen
The breach is linked to an April 8 incident, in which a known cybercrime group going by the name USDoD claimed to have access to the personal data of 2.9 billion people in the US, UK and Canada, and that it was selling the information for $3.5 million, according to a class action complaint. USDoD is believed to have obtained the database from another threat actor using the alias “SXUL.”
The data was allegedly stolen from National Public Data, also known as Jericho Pictures, and the perpetrators claimed it contained records of all individuals in the three countries. At the time, malware website VX-Underground said the data dump did not include information on people who use data opt-out services.
“Not everyone who used some kind of data opt-out service was in attendance,” the post on X read.
See also: Nearly 10 billion passwords leaked in biggest breach in history
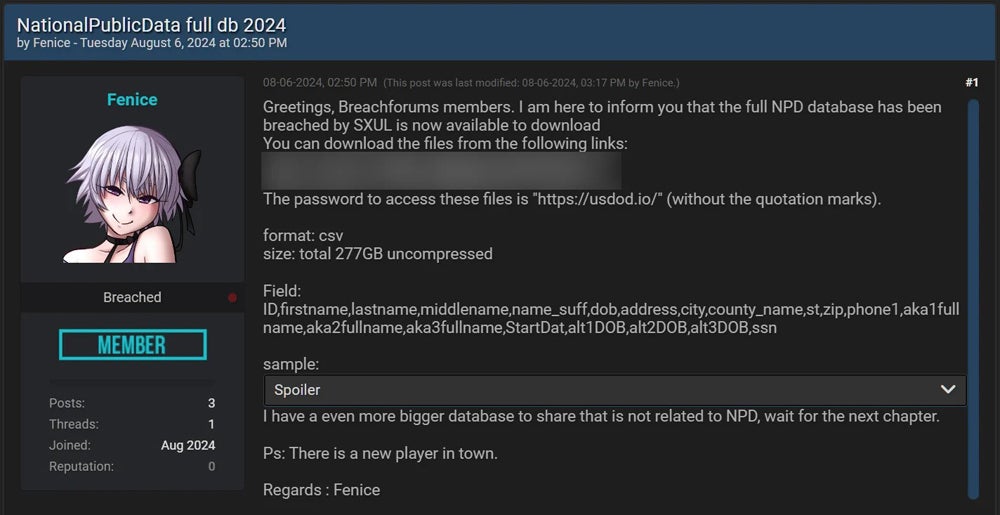
Since then, many cybercriminals have posted various samples of this data, many of which were different entries and contained phone numbers and email addresses. However, earlier this month, a user named “Fenice” leaked 2.7 billion unencrypted records in the form of two csv files totaling 277 GB on a dark web site called “Breached.” These did not contain any phone numbers or email addresses, and Fenice said the data came from SXUL.
A sister site of National Public Data may have provided an entry point.
According to an investigation by Krebs on Security, the hackers may have gained initial access to the national public data records via sister service RecordsCheck, another background check service.
Until August 19th, “recordscheck.net” hosted an archive called “members.zip” that contained source code for various components of the site, including the administrator, as well as plain text usernames and passwords. According to the archive, all users of the site were given the same six-character password by default, but many users never changed their passwords.
Moreover, recordscheck.net “looks similar to nationalpublicdata.com, even the login page is identical,” Krebs wrote. National Public Data founder Salvatore “Sal” Bellini later told Krebs that “members.zip” was “an older version of the site that contained non-working codes and passwords” and that RecordsCheck would cease operations “in the next week or so.”
Beyond the plaintext passwords, there’s other evidence that RecordsCheck provided an entry point into Verini’s assets. Krebs said RecordsCheck ran background checks on people by matching their records with a National Public Data database from a data broker called USInfoSearch.com. In November, it was revealed that a number of USInfoSearch accounts had been hacked and were being used by cybercriminals.
Not all of the 2.7 billion leaked records are accurate or unique, but some are.
Because each individual has multiple records associated with them, one for each previous address, this breach does not expose the information of 2.7 billion different people. Additionally, according to BleepingComputer, some affected individuals confirmed that the SSNs associated with their information in the data dump were incorrect.
BleepingComputer also found that some of the records did not list current addresses for individuals, suggesting that at least some of the information is out of date, but others confirmed that the data contained legitimate information for people and their families, including those who have passed away.
The class action complaint adds that National Public Data collects and profiles billions of people’s personally identifiable information from undisclosed sources, meaning those affected may not have knowingly provided their data. Anyone living in the United States is likely affected by this breach.
Several websites have been set up to allow individuals to check whether their information has been exposed in a national public data breach, including npdpentester.com and npdbreach.com.
Experts TechRepublic spoke to suggested that individuals affected by the breach should consider monitoring or freezing their credit reports and remain vigilant against phishing attacks targeting their emails and phone numbers.
Companies must ensure that all personal data they hold is encrypted and stored securely, and they should also implement other security measures such as multi-factor authentication, password managers, security audits, employee training, and threat detection tools.
See also: How to avoid data breaches
TechRepublic has reached out for answers to Florida-based National Public Data, which is currently under investigation by Schubert Jonckheer & Kolbe LLP.
Plaintiff Christopher Hoffman said he received notice from his identity theft protection service provider on July 24 that his personal information had been leaked and made public on the dark web as a direct result of the nationalpublicdata.com breach.
What security experts are saying about the breach
Why are national public data records so valuable to cybercriminals?
John Miller, CEO and co-founder of anti-ransomware platform Halcyon, said the value of a national public data record from a criminal’s perspective comes from the fact that it is collected and organized.
“Much of this information is already available to attackers, but it would have taken a lot of money and effort to collect similar data, so NPD has done them a favor by making it easier,” he said in an email to TechRepublic.
See also: How organizations can deal with data breaches
Oren Coren, CPO and co-founder of security platform Veriti, added that information about deceased individuals could be reused for malicious purposes. He wrote in an email to TechRepublic: “With this ‘starting point,’ an individual could try to create a birth certificate, voting certificate, etc., which would be valid because some of the necessary information would be there, most importantly the Social Security number.”
How can we stop data aggregators from being breached?
Paul Bischoff, a consumer privacy advocate at tech research firm Comparitech, told TechRepublic in an email, “Background check companies like National Public Data are essentially data brokers, collecting as much personally identifiable information as they can and selling it to anyone who will pay for it. They collect a lot of data without the data subjects’ knowledge or consent, and most people have no idea what National Public Data is or what it does.”
“Data brokers need stronger regulation and transparency. They should be required to notify data subjects when their information is added to their databases, limit web scraping, and allow data subjects to view, change, and delete their data.”
“National Public Data and other data brokers should be required to show data subjects the origin of their information so people can take proactive steps to protect their privacy at the source. Furthermore, any breached data cannot have been unencrypted.”
Miller added, “The monetization of our personal information, including the information we choose to make public, goes far beyond the legal protections that govern who can collect what, how it can be used, and most importantly, who is responsible for protecting it.”
Can businesses and individuals prevent themselves from becoming victims of a data breach?
Chris Deibler, vice president of security at security solutions provider DataGrail, said many of the cyber hygiene principles available to businesses and individuals would not have been of much use in this case.
“In this environment, we are reaching the limits of what individuals can reasonably do to protect themselves, and real solutions will need to come at the corporate and regulatory levels, including standardizing data privacy regulations through international treaties,” he told TechRepublic in an email.
“The current balance of power is not in favor of the individual. While the GDPR and the various state and national regulations enacted online are good steps, it is clear that the prevention and consequence model currently in place will not stop the mass aggregation of data.”


